Active Directory (AD) is a critical component in modern IT infrastructures, providing a centralized way to manage users, devices, applications, and security policies across an enterprise network. Originally developed by Microsoft, it has become the foundation for identity and access management (IAM) in Windows environments. Businesses of all sizes rely on it to enforce security measures, simplify user authentication, and improve administrative efficiency. This article provides a deep dive into how Active Directory works, its key components, security best practices, and strategies for effective management.
Setting Up a HomeLab with VirtualBox: A Step-by-Step Guide
The Role of Active Directory in Enterprise IT
Active Directory is more than just a directory service. It serves as a comprehensive identity management solution that streamlines user authentication and authorization. By implementing AD, organizations gain a structured way to handle permissions and security policies. IT administrators use it to define which users and devices have access to network resources, ensuring data security and operational efficiency.
One of the most significant advantages of AD is its ability to enable Single Sign-On (SSO). Instead of requiring employees to remember multiple passwords for different applications and services, AD provides seamless authentication using a single set of credentials. This reduces password fatigue, lowers the risk of credential compromise, and enhances user productivity.
Another critical function is Group Policy, which allows administrators to enforce rules and configurations across multiple devices. This ensures consistency in security settings, application installations, and other operational policies. Whether managing password policies, software updates, or user access restrictions, Group Policy simplifies network administration.
Core Components of Active Directory
Active Directory consists of several integral components that work together to maintain an organized and secure IT environment. At the heart of AD is the domain, which acts as the fundamental administrative unit. A domain contains objects such as users, computers, printers, and groups. Domains are further structured into trees and forests to accommodate complex organizational needs.
A Domain Controller (DC) is the server that stores and manages AD data, handling authentication and authorization requests. Enterprises typically deploy multiple domain controllers for redundancy, ensuring high availability and fault tolerance. The Global Catalog (GC) enhances performance by maintaining an index of AD objects, making searches and queries more efficient.
Organizational Units (OUs) provide a way to logically group users and devices within a domain. IT administrators use OUs to delegate administrative control, applying Group Policy Objects (GPOs) selectively to different departments, teams, or device categories. This structure simplifies management and enhances security by limiting access to specific resources based on job roles.
Another key feature is Kerberos authentication, which secures network communication by issuing time-sensitive tickets for authentication. This process strengthens security by reducing reliance on plaintext passwords and ensuring encrypted credential exchanges.
Computer Management AD RSAT Tools
Security Best Practices for Active Directory
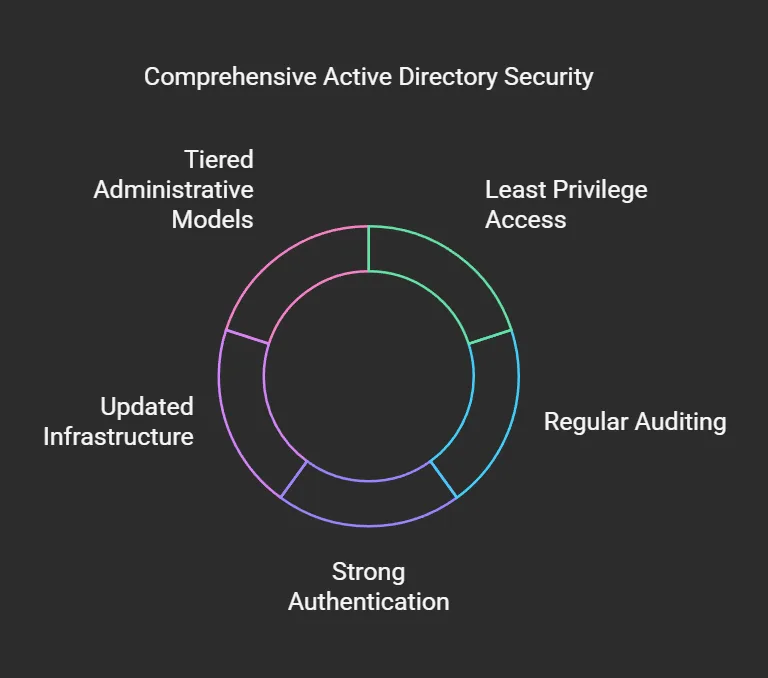
Given its central role in identity management, securing Active Directory is a top priority for IT teams. A compromised AD environment can lead to unauthorized access, data breaches, and severe operational disruptions. Implementing robust security measures helps mitigate these risks and safeguards enterprise assets.
One of the fundamental security measures is enabling least privilege access. Instead of granting excessive permissions, administrators should assign only the minimum level of access necessary for users to perform their tasks. This principle reduces the attack surface and limits potential damage in case of a security breach.
Regularly auditing AD logs is another crucial security practice. Monitoring user logins, failed authentication attempts, and privilege escalations helps detect suspicious activities early. IT teams should configure Security Information and Event Management (SIEM) systems to collect and analyze log data, providing real-time alerts on potential threats.
Enforcing strong authentication methods strengthens AD security. Implementing Multi-Factor Authentication (MFA) adds an extra layer of protection by requiring users to verify their identity using a secondary method, such as a mobile app or hardware token. Additionally, deploying Privileged Access Workstations (PAWs) ensures that administrators perform high-risk tasks in a secure, isolated environment, reducing exposure to malware and phishing attacks.
Keeping AD infrastructure updated is equally critical. Regularly patching Domain Controllers and other AD-related components prevents exploits from targeting known vulnerabilities. Organizations should also implement tiered administrative models, separating high-privilege accounts from regular user accounts to minimize risk.
Strategies for Effective Active Directory Management
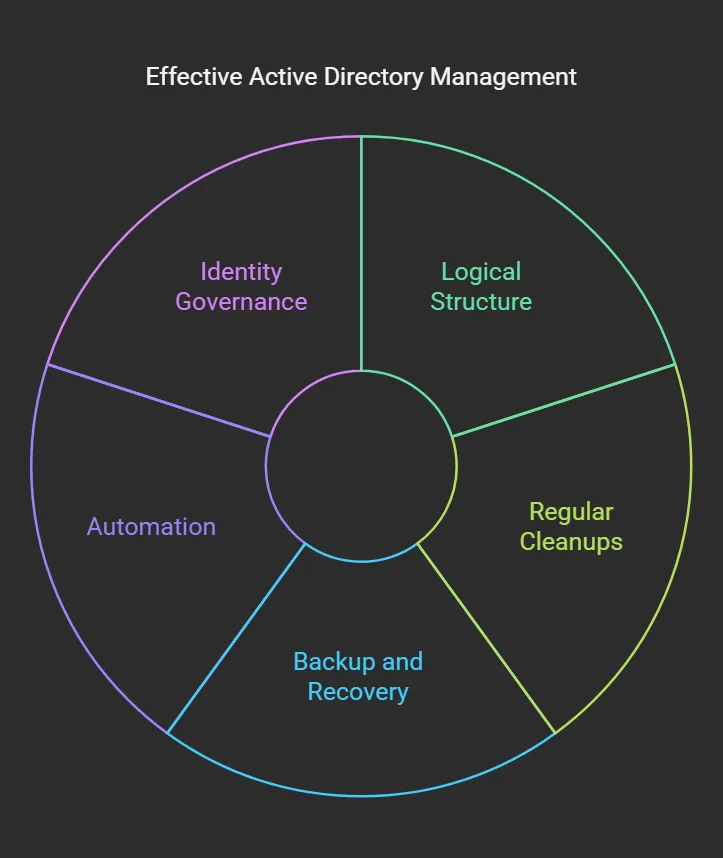
Managing Active Directory efficiently requires a proactive approach that balances security, performance, and operational flexibility. A well-organized AD structure reduces complexity, making it easier for IT teams to administer and troubleshoot issues.
Designing a logical AD structure is the first step to effective management. Instead of creating excessive OUs and groups, administrators should maintain a streamlined hierarchy that aligns with business needs. Overcomplicating the AD layout leads to management overhead and increases the likelihood of misconfigurations.
Regularly performing cleanups helps maintain a healthy AD environment. Removing inactive accounts, outdated computer objects, and redundant group memberships prevents clutter and reduces security risks. Automating these tasks with PowerShell scripts or third-party AD management tools ensures consistency and efficiency.
Implementing backup and recovery solutions is essential for disaster preparedness. A corrupted or misconfigured AD environment can severely impact business operations. Regularly backing up System State data and testing restoration processes ensures that organizations can recover quickly in case of failures.
Using automation enhances efficiency and reduces human errors. IT teams can automate user provisioning and de-provisioning workflows to ensure that employees gain access to resources immediately upon joining and lose access upon departure. Integrating AD with Identity Governance solutions further improves compliance by enforcing access review policies.
Case Study
Ticket 1: Creating a Group in Active Directory
To create a group in Active Directory, start by opening Server Manager.
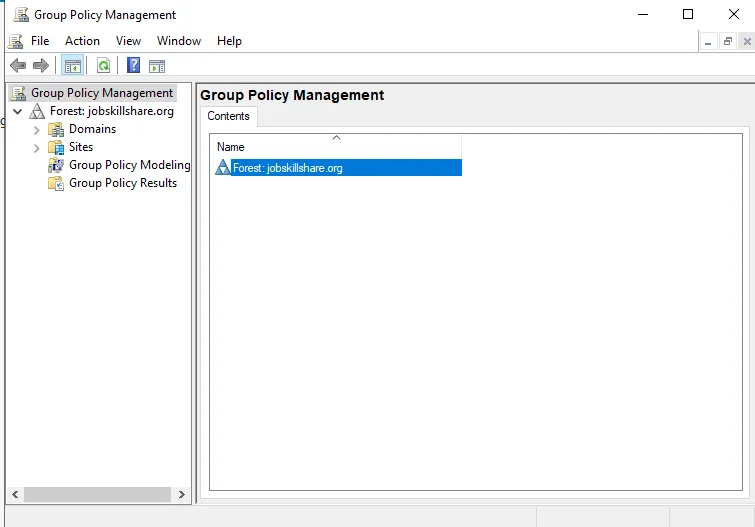
From the dashboard, navigate to Tools, then select Group Policy Management. Once inside, locate the domain and expand it to find the Default Domain Policy. Right-click on it and choose Edit to access the Group Policy Management Editor.
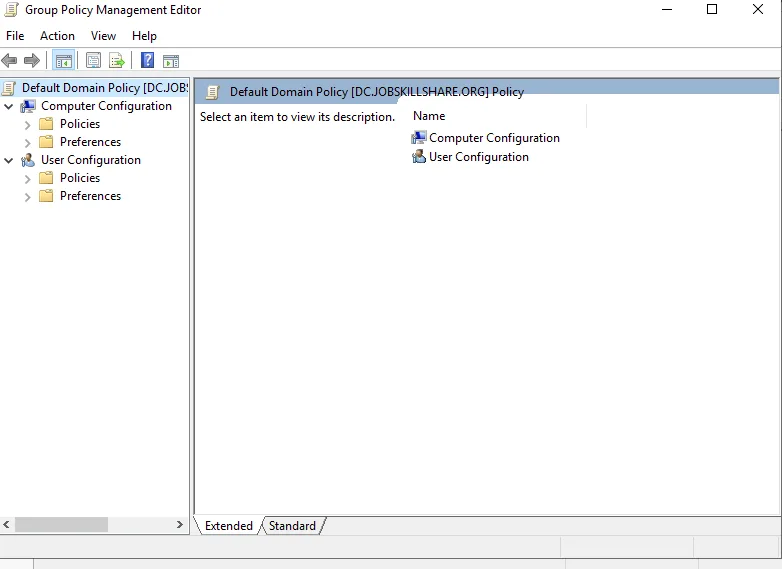
Within the Group Policy Management Editor, navigate to Computer Configuration and expand the Policies section. Here, continue by expanding Windows Settings, then move into Security Settings.
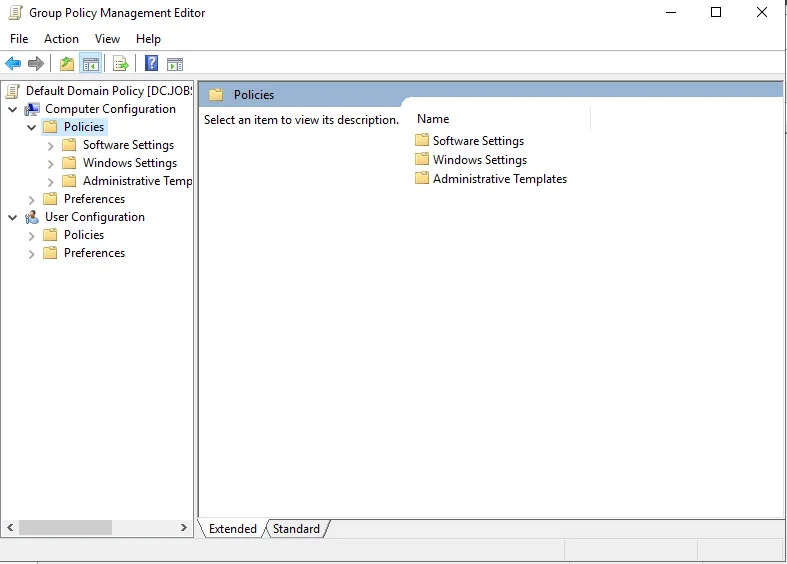
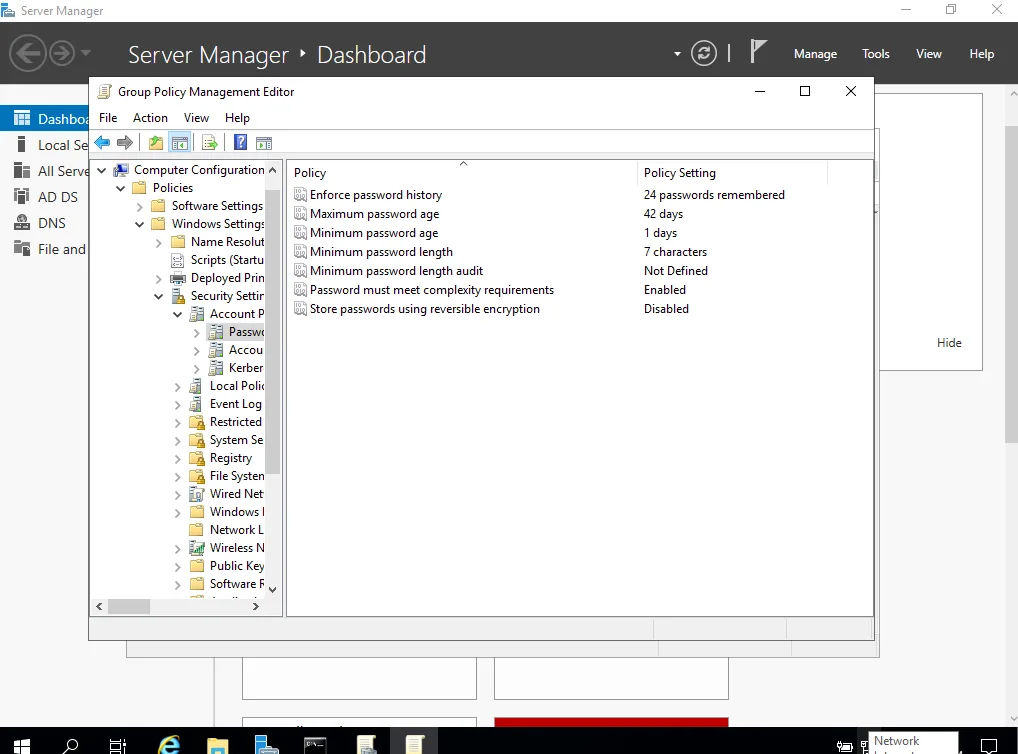
Under this section, locate Account Policies and open Password Policy to review the existing security policies. If the settings do not align with security best practices, modifications should be made accordingly.
To verify password policies from the command line, open CMD and execute the following command:
net accounts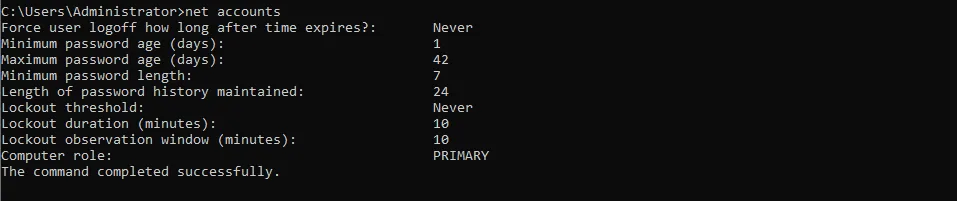
This command provides an overview of existing account policies, including password expiration, length requirements, and lockout thresholds. If a lockout policy has not yet been configured, it is vital to establish one to prevent brute-force attacks.
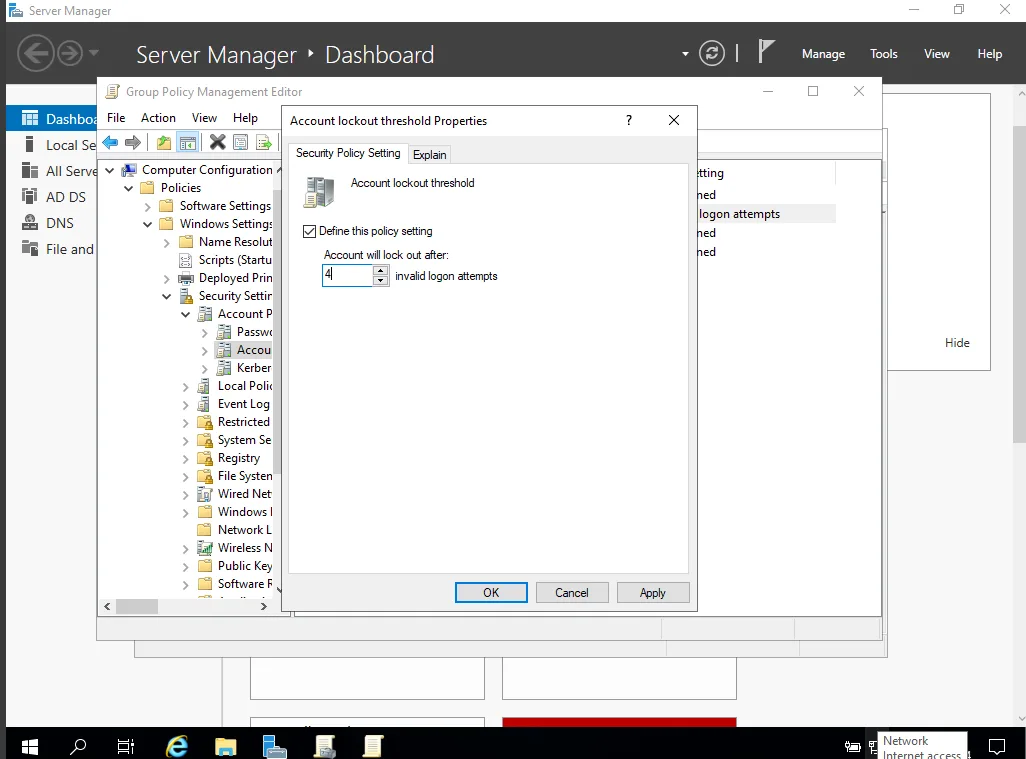
To configure an account lockout policy, return to the Security Settings section and select Account Lockout Policy. Within this section, locate Lockout Account Threshold and set it to 4 incorrect login attempts. Apply the changes by clicking OK. This policy ensures that accounts get temporarily locked after too many failed login attempts, preventing unauthorized access.
Once the policy settings have been adjusted, update the Group Policy to enforce the changes. Open CMD again and run the following commands:
gpupdate
net accounts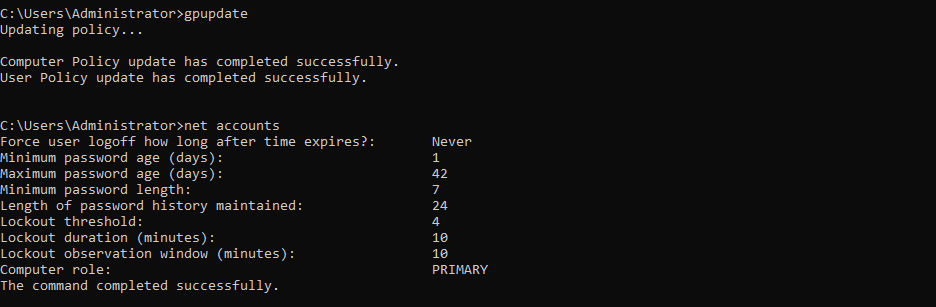
Executing these commands ensures that the system adheres to the new policies immediately.
Ticket 2: Enabling Remote Desktop Connection
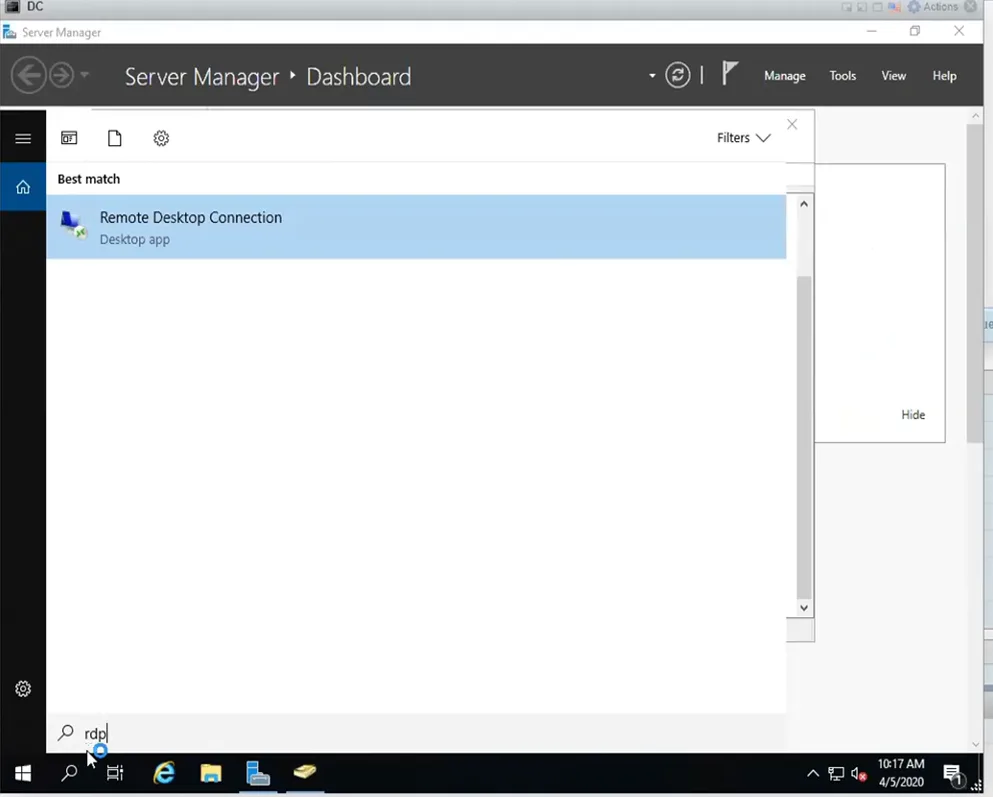
Remote Desktop Protocol (RDP) is an essential tool for system administrators, enabling remote access to servers within the Active Directory network. Before establishing a remote session, test if Remote Desktop Connection (RDP) is enabled by attempting to log in from another machine on the same network. If access is denied, remote access permissions may need to be enabled.
To enable Remote Desktop Connection, navigate to the System settings. Within this panel, scroll down and locate the System Info section.
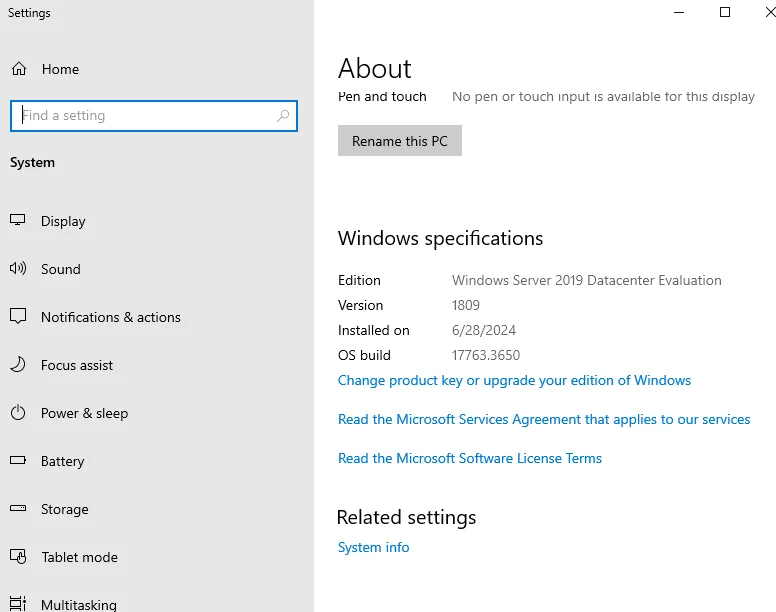
Clicking on this will provide access to advanced configuration settings. Proceed by selecting Remote Settings and enabling Allow remote connections to this computer. Once this option is checked, confirm the settings by clicking Apply and OK.
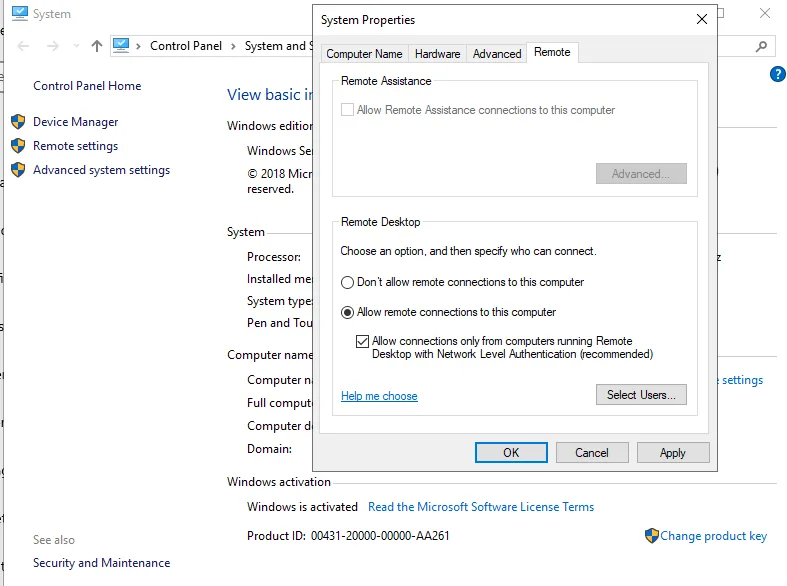
Configuring RDP within an Active Directory environment allows administrators to manage multiple machines efficiently without needing physical access. However, for security purposes, it is also recommended to configure Network Level Authentication (NLA) to restrict unauthorized access attempts.
With these configurations in place, Active Directory policies are not only securely managed but also optimized for seamless administration. By following this structured approach, system administrators can ensure that their home lab environments reflect the security and efficiency of enterprise-grade networks.
Active Directory is a powerful tool for managing enterprise environments, enabling system administrators to enforce security policies, manage users, and configure remote access. This guide has covered the essential steps for setting up security policies within Group Policy Management and configuring Remote Desktop Connection to facilitate remote server management. These foundational practices strengthen both security and usability in an Active Directory-controlled network, making them essential for any IT professional managing Windows Server environments.
What is Active Directory and why is it important?
Active Directory (AD) is a Microsoft-developed directory service used in Windows domain networks to manage users, computers, and security policies. It enables centralized authentication, access control, and policy enforcement, making it essential for IT environments.
How do I create and manage groups in Active Directory?
Groups in AD can be created using Server Manager by navigating to Group Policy Management and modifying the Default Domain Policy. Groups help administrators efficiently manage permissions for multiple users and resources.
What are Group Policy Objects (GPOs) and how do they work?
GPOs are policies in Active Directory that define security settings, software installation, and configurations across an organization. They ensure consistent settings are applied to users and computers in a domain.
How can I enable and secure Remote Desktop Protocol (RDP) in Active Directory?
RDP can be enabled by accessing System Settings and allowing remote connections. To enhance security, it’s recommended to enable Network Level Authentication (NLA) and restrict access through GPOs.
What are some best practices for securing Active Directory?
Best practices include enabling strong password policies, enforcing account lockout policies, using least privilege access, regularly updating GPOs, and monitoring event logs for security threats.